What is a Security Configuration Review?
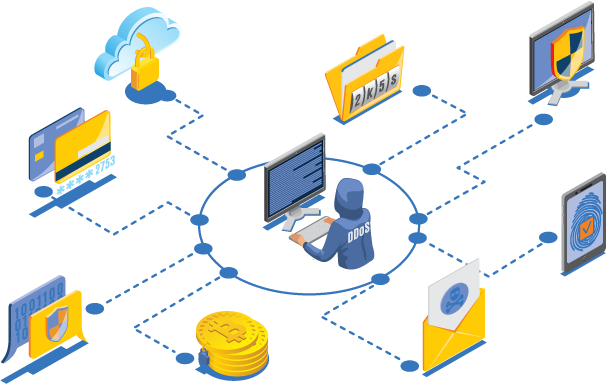
The Security Configuration Review intends to provide an appropriate level of security to the portion of the network that has threats by identifying portions and rating each portion based on the threat it can cause.. to identify a portion of the network, assign a threat rating to each portion, and apply an appropriate level of security. It will identify threats to the network, network resources, and data. The primary goal is to strike a reasonable balance between security and required network access.
An organization's IT policy should ensure that security is always kept in mind when configuring network devices. Security flaws are one of the most common vulnerabilities that criminal hackers seek to exploit. As a result, organizations must conduct Security Configuration Reviews of network and app infrastructure on a quarterly basis to ensure that security measures are implemented when building and installing computers and network devices, thereby reducing unnecessary cyber vulnerabilities.
The importance of regularly assessing system configurations
It's critical to make sure your organization's cyber security keeps up with the rapid pace of business growth and digital transformation. New systems, applications, and devices can introduce security risks, allowing an attacker to gain access to critical data and assets on your network. Many devices come with inadequate default settings.
Benefits:
- Reduction in risk of the network device compromise, and subsequent loss of revenue & productivity.
- Extends the connectivity to achieve business objectives without sacrificing security.
- Verification of the operating condition and the effectiveness of your security configuration and rule sets.
- Establishment of a baseline for best security practices.
- Ensuring the investment in security to increase effectiveness.

